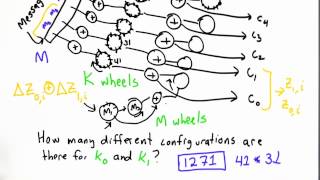
03. weak-key distinguishers for aes
Published 3 years ago • 230 plays • Length 32:50Download video MP4
Download video MP3
Similar videos
-
 12:57
12:57
cryptanalysis 9.4: chosen-key distinguishers of aes
-
 13:12
13:12
aes-ctr cryptography: reused key weakness - hackthebox cyber apocalypse ctf
-
 1:13
1:13
weakness in keys solution - applied cryptography
-
 11:06
11:06
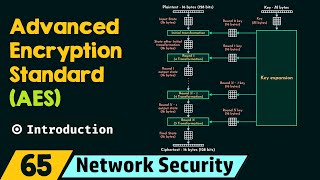
introduction to advanced encryption standard (aes)
-
 37:02
37:02
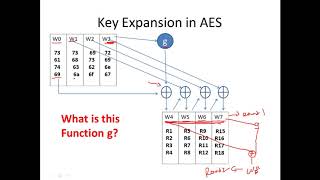
aes iii - advanced encryption standard - introduction , key expansion in aes cyber security cse4003
-
 9:11
9:11
one encryption standard to rule them all! - computerphile
-
 5:51
5:51
how to design a completely unbreakable encryption system
-
 18:02
18:02
aes gcm (advanced encryption standard in galois counter mode) - computerphile
-
 0:50
0:50
weakness in keys - applied cryptography
-
 14:56
14:56
aes key expansion
-
 13:24
13:24
aes encryption and decryption
-
 30:29
30:29
aes (advance encryption standard ) complete explanation
-
 14:14
14:14
aes explained (advanced encryption standard) - computerphile
-
 24:23
24:23
26. improvements to quantum search techniques for block-ciphers, with applications to aes
-
 1:02
1:02
aes round
-
 18:37
18:37
weak keys in reduced aegis and tiaoxin
-
 17:34
17:34
learn cryptography | part 3 - encryption algorithms and keylengths
-
 18:26
18:26
improved key recovery attacks on reduced round aes with practical data and memory complexities
-
 54:54
54:54
block cipher standards (aes) (contd.)
-
 15:37
15:37
aes: how to design secure encryption