5 gathering breached credentials with weleakinfo
Published 3 years ago • 953 plays • Length 4:28Download video MP4
Download video MP3
Similar videos
-
 3:58
3:58
information gathering using weleakinfo | #weleakinfo tutorial
-
 4:21
4:21
best weleakinfo alternative
-
 1:50
1:50
billions in taxpayer money at stake in second 5g network deployment, says khairy
-
 36:04
36:04
queryable data encryption
-
 19:22
19:22
27 mastering ethical hacking the breached credentials | educate everyone4free
-
![locate breached account data with h8mail [tutorial]](https://i.ytimg.com/vi/z8G_vBBHtfA/mqdefault.jpg) 13:57
13:57
locate breached account data with h8mail [tutorial]
-
 5:09
5:09
3 great website traffic sources you're probably not using
-
 7:26
7:26
the u.s. lost the 5g race…after an immigrant was forced to leave
-
![find vulnerable services & hidden info using google dorks [tutorial]](https://i.ytimg.com/vi/u_gOnwWEXiA/mqdefault.jpg) 13:37
13:37
find vulnerable services & hidden info using google dorks [tutorial]
-
 0:53
0:53
how to read blocked, blurred, or locked content or text on sites
-
 20:16
20:16
breaking: fcc releases production version of the broadband data collection fabric
-
 57:36
57:36
sectalks syd0x37 (55th) - password cracking in 2020 (or) why does this still work?
-
 0:44
0:44
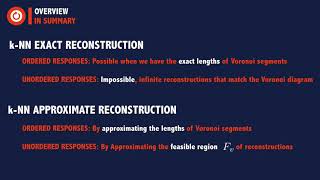
data recovery on encrypted databases with k-nearest neighbor query leakage
-
 1:01
1:01
tool weleakinfo hack / information/user/email 2022 tool
-
 1:03
1:03
privacy-enhancing technologies for healthcare data analysis
-
 0:35
0:35
jm3kfbey9l0809445 mazda cx 5 2020
-
 8:01
8:01
leaked top secret documents reveal how illicit funds are moved around the world | 7.30
-
 3:23
3:23
turbotax credential stuffing - security byte
-
 2:17
2:17
5g fixed wireless access: a solution for digital divide
-
 6:34
6:34
privacy-aware cross-platform service recommendation based on enhanced locality-sensitive hashing
-
 1:03:03
1:03:03
find your content gaps: 5 sources reveal the holes in your content marketing