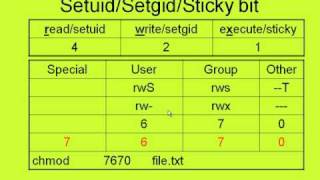
abuse elevation control mechanism setuid and setgid
Published 1 year ago • 42 plays • Length 1:01Download video MP4
Download video MP3
Similar videos
-
 5:15
5:15
linux - exploiting setuid
-
 12:51
12:51
linux suid vulnerability demonstration
-
 11:43
11:43
gaining root access on linux by abusing suid binaries (privilege escalation)
-
 40:42
40:42
linux red team privilege escalation techniques - kernel exploits & sudo permissions
-
![[hindi] || t1166: setuid and setgid || linux persistence || mitre att&ck || lab 09](https://i.ytimg.com/vi/xNlrMQ32toE/mqdefault.jpg) 15:47
15:47
[hindi] || t1166: setuid and setgid || linux persistence || mitre att&ck || lab 09
-
 0:16
0:16
a day in the life of cyber security | soc analyst | penetration tester | cyber security training
-
 17:03
17:03
sads: setuid and setguid and sticky bit (linux file permissions)
-
 0:19
0:19
ethical hacking guide for beginners | learn ethical hacking #ytshortsindia #ethicalhacking #shorts
-
 0:32
0:32
when you first time install kali linux for hacking 😄😄 #hacker #shorts
-
 0:23
0:23
occupytheweb wrote the following useful books for hackers
-
 0:49
0:49
apple will pay hackers $1,000,000 for this bug bounty 😳
-
 0:51
0:51
cybersecurity or software engineering? 👩🏻💻 #shorts
-
 0:52
0:52
cybersecurity certifications don't equal 6 figures
-
 0:19
0:19
hacking tools #security #cybersecurity #hacking #computersecurity #network #shorts
-
 3:06
3:06
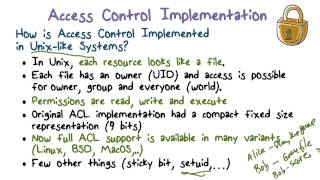
access control implementation setuid
-
 0:56
0:56
hacking linux with these simple commands pt:1