airdrop man-in-the-middle attack (usenix security '19)
Published 5 years ago • 4.4K plays • Length 1:50Download video MP4
Download video MP3
Similar videos
-
 19:26
19:26
usenix security '19 - a billion open interfaces for eve and mallory: mitm, dos, and tracking
-
 8:47
8:47
man-in-the-middle attack (mitm) live demonstration - wi-fi hacks | wireshark
-
 15:24
15:24
iphone and android wifi man-in-the-middle attack // python scapy scripts for attacking networks
-
 11:35
11:35
arp poisoning | man-in-the-middle attack
-
 6:01
6:01
helium mobile outdoor wifi hotspot update | mntd. fi pro
-
 5:50
5:50
browser tips: how to prevent any man-in-the-middle attack even in the most hostile environment
-
 10:38
10:38
claim cyber finance airdrop with trust wallet
-
 11:49
11:49
usenix security '21 - disrupting continuity of apple's wireless ecosystem security: new tracking
-
 12:06
12:06
usenix security '21 - privatedrop: practical privacy-preserving authentication for apple airdrop
-
 7:10
7:10
man in the middle attack mitm using wireshark and ettercap | full tutorial for beginner 2022
-
 1:20
1:20
what is a man-in-the-middle attack? (in about a minute)
-
 11:54
11:54
how to set up a man in the middle attack | free cyber work applied series
-
 9:31
9:31
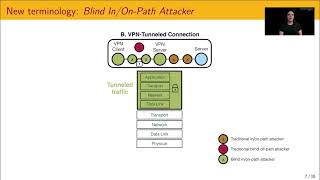
usenix security '21 - blind in/on-path attacks and applications to vpns
-
 19:07
19:07
how hackers sniff (capture) network traffic // mitm attack
-
 3:54
3:54
man-in-the-middle attack explained: how can you to prevent mitm attack
-
 1:21
1:21
man in the middle (mitm) attack ios
-
 5:52
5:52
what is a man-in-the-middle attack?
-
 28:35
28:35
usenix security '16 - armageddon: cache attacks on mobile devices
-
 11:30
11:30
bettercap arp spoofing🕵🏼man in the middle - mitm 15.2