analyzing logs and exploiting php book store - tryhackme owasp top 10
Published 3 years ago • 2.8K plays • Length 10:51Download video MP4
Download video MP3
Similar videos
-
 16:48
16:48
finding security misconfigurations in a website - comptia pentest tryhackme owasp top 10
-
 15:36
15:36
explaining insecure deserialization vulnerability - comptia pentest tryhackme owasp
-
 33:53
33:53
tryhackme - owasp top 10 walkthrough p.1 (comptia pentest )
-
 15:31
15:31
practical malware phishing email analysis | tryhackme greenholt phish
-
 13:14
13:14
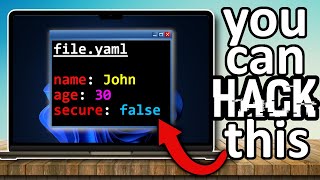
capture the flag: hacking yet another markup language
-
 9:32
9:32
ollama and langchain.js for rag | complete code example
-
 12:20
12:20
command injection vulnerability explained | tryhackme owasp top 10 walkthrough
-
 33:36
33:36
owasp top 10 - 2021 tryhackme walkthrough - a hands-on guide to web security threats
-
 14:18
14:18
owasp top 10 api vulnerabilities explained | part four | tryhackme
-
 17:40
17:40
owasp top 10 api vulnerabilities explained | part one | tryhackme
-
 36:11
36:11
the pyramid of pain explained | complete tutorial | tryhackme