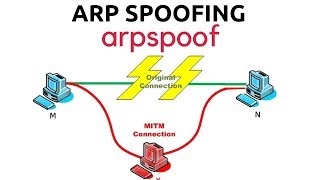
arp spoofing
Published 4 years ago • 12K plays • Length 5:20Download video MP4
Download video MP3
Similar videos
-
 9:58
9:58
arp poisoning and port mirroring attacks
-
 28:23
28:23
home lab 14: arp & dns spoofing with bettercap - beginner's step-by-step guide
-
 0:54
0:54
arp poisoning explained
-
 11:35
11:35
arp poisoning | man-in-the-middle attack
-
 2:52
2:52
using arp poisoning to capture traffic from a target on the network
-
 20:06
20:06
arp poisoning and defense strategies
-
 16:46
16:46
arp poisoning or arp spoofing attack - explanation & demonstration
-
 5:25
5:25
dns spoofing using ettercap
-
 4:24
4:24
how hackers arp-spoof to intercept passwords over wi-fi
-
 7:48
7:48
demo tấn công arp poisoning
-
 10:02
10:02
arp spoofing with arpspoof - mitm
-
 9:07
9:07
how to do arp poisoning or arp spoofing? (practical)
-
 6:53
6:53
get usernames and passwords with ettercap, arp poisoning (cybersecurity)
-
 1:32
1:32
arp spoofing attack explained
-
 3:09
3:09
what is arp spoofing?
-
 6:24
6:24
the complete guidance of arp spoofing and arp poisoning | cissp | cyber security
-
 8:18
8:18
mitm attack | arp spoofing | arp poisoning in kali linux
-
 5:12
5:12
spoofing - n10-008 comptia network : 4.2
-
 10:41
10:41
arp spoofing
-
 7:24
7:24
arp spoofing 🔥🔥
-
 56:38
56:38
3) network assessment for arp spoofing
-
 32:29
32:29
try hack me - l2 mac flooding & arp spoofing