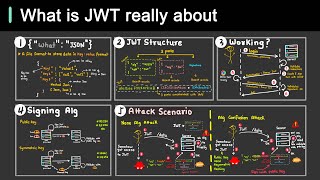
attacking and defending jwt tokens: the ultimate guide - leo juszkiewicz, palo alto networks
Published 1 year ago • 243 plays • Length 37:24Download video MP4
Download video MP3
Similar videos
-
 14:53
14:53
what is jwt and why should you use jwt
-
 1:07
1:07
how does jwt work
-
 5:14
5:14
why is jwt popular?
-
 11:53
11:53
difference between cookies, session and tokens
-
 12:13
12:13
learn how to hack jwt token | multiple way to exploit jwt token
-
 6:30
6:30
json web token hacking
-
 16:33
16:33
introduction to jwt attacks
-
 7:39
7:39
attacking jwt for beginners!
-
 0:51
0:51
understanding jwt: json web tokens explained in 45 seconds
-
![what are json web tokens? jwt auth explained [tutorial]](https://i.ytimg.com/vi/x5gLL8-M9Fo/mqdefault.jpg) 1:41:00
1:41:00
what are json web tokens? jwt auth explained [tutorial]
-
 0:49
0:49
jwt
-
 4:10
4:10
how to build a full-stack authentication system using json web tokens
-
 18:51
18:51
an improved practical key mismatch attack against ntru
-
 5:15
5:15
demystifying jwk & jwks | keycloak jwks endpoint
-
 1:00
1:00
what is a jwt? 🆔⌛
-
 46:46
46:46
json web tokens crash course - jwt tokens explained