secure code warrior explainer video - insufficient anti-automation
Published 6 years ago • 1.6K plays • Length 3:31Download video MP4
Download video MP3
Similar videos
-
 17:39
17:39
how ai companies use the cloud, despite security risks
-
 45:07
45:07
know the enemy: what execs need to understand to secure their software supply chain
-
 3:05
3:05
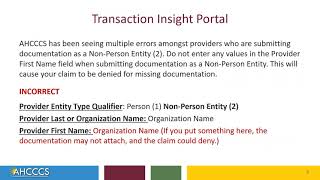
transaction insight portal - common errors for non-person entity users
-
 20:48
20:48
new operator: apollon & everything you need to know
-
 6:47
6:47
exploiting nosql operator injection to bypass authentication | web security academy | portswigger
-
 1:31
1:31
haptic-act: bridging human intuition with compliant robotic manipulation via immersive vr
-
 3:49
3:49
insufficient transport layer protection | owasp top 10 explainer video | secure code warrior
-
![javascript nullish operators - coalescing and optional chaining // ?? ?.[]()](https://i.ytimg.com/vi/i6CsAoSnalQ/mqdefault.jpg) 5:49
5:49
javascript nullish operators - coalescing and optional chaining // ?? ?.[]()
-
 1:02:26
1:02:26
exclusive: meet tesla bot’s biggest competitor | brett adcock figure
-
 27:17
27:17
israel lebanon ground invasion believed imminent as tanks mass at border
-
 15:23
15:23
a graphene transistor breakthrough?
-
 24:49
24:49
accelerate threat detection using the mitre att&ck framework
-
 57:04
57:04
how attackers move laterally in your network
-
 4:14
4:14
privacy and auditability in the ai supply chain | tobin south | mit 2024
-
 31:10
31:10
technique to find no recoil/no spread /accuracy
-
 54:57
54:57
pick a framework, not a tool: the value of being a trusted prescriber
-
 24:04
24:04
secure software leasing without assumptions
-
 55:18
55:18
att&cking your enterprise: adversary detection pipelines & adversary simulation
-
 14:00
14:00
usenix security '23 - smart learning to find dumb contracts
-
![10 techniques to understand code you don’t know - jonathan boccara [accu 2019]](https://i.ytimg.com/vi/tOOK-VsWU-I/mqdefault.jpg) 59:00
59:00
10 techniques to understand code you don’t know - jonathan boccara [accu 2019]
-
 25:07
25:07
enabling real-time secure connectivity to the industrial edge with single-pair ether... jason murphy