breaking and repairing gcm security proofs
Published 12 years ago • 967 plays • Length 18:44Download video MP4
Download video MP3
Similar videos
-
 1:02:42
1:02:42
session on security proofs
-
 16:02
16:02
what is gcm? galois counter mode (of operation) (usually seen as aes-gcm)
-
 3:15
3:15
galois/counter mode (gcm) and gmac
-
 3:19
3:19
the insider - rfeye guard, a tscm solution - detect. locate. protect.
-
 23:41
23:41
linear repairing codes and side channel attacks
-
 4:03
4:03
104 galois/counter mode (gcm) and gmac: get a gut level understanding
-
 10:30
10:30
how to fix device with play protect verified
-
 7:01
7:01
samsung a22 5g(a226b u6) imei repair new security by chimera | root file 100%tasted link description
-
 7:46
7:46
xiaomi •disable rsa security | hardware method
-
 5:31
5:31
how to patch management for the device
-
 20:51
20:51
the multi-user security of gcm, revisited: tight bounds for nonce randomization
-
 3:18
3:18
what is guardgo browser extension? hijacker analysis & removal
-
 1:41
1:41
learn how to fix gnferror during lvs run | synopsys
-
 31:46
31:46
breaking the identity perimeter: an attacker's perspective
-
 30:34
30:34
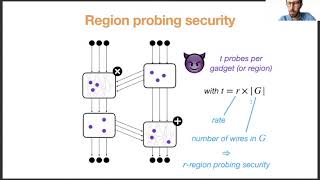
probing security through input-output separation and revisited quasilinear masking
-
 25:37
25:37
fse 2018 - reconsidering the security bound of aes-gcm-siv