breaking masked implementations with many shares on 32-bit software platforms: or when the secu...
Published 2 years ago • 108 plays • Length 23:41Download video MP4
Download video MP3
Similar videos
-
 1:23:50
1:23:50
session on masking schemes and their analysis
-
 24:14
24:14
pyjamask: block cipher and authenticated encryption with highly efficient masked implementation
-
 14:49
14:49
masking aes with d 1 shares in hardware
-
 21:01
21:01
reducing a masked implementation’s effective security order with setup manipulations
-
 2:47
2:47
remove unwanted signal with mask channel tool
-
 1:01:20
1:01:20
secret sharing 1 (crypto 2023)
-
 21:33
21:33
bsidestlv 2024 - gotta catch 'em all: phishing, smishing, and the birth of scanmysms
-
 1:06:15
1:06:15
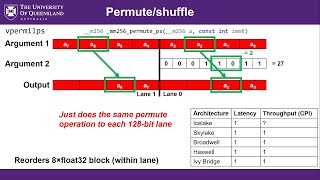
simd and vectorization using avx intrinsic functions (tutorial)
-
 31:43
31:43
secure and efficient software masking on superscalar pipelined processors
-
 24:36
24:36
improved masking for tweakable blockciphers with applications to authenticated encryption
-
 55:32
55:32
partial session on high order masking
-
 20:09
20:09
a side-channel attack on a masked ind-cca secure saber kem implementation
-
 22:37
22:37
revealing the weakness of addition chain based masked sbox implementations
-
 3:06
3:06
multi-arm payload manipulation via mixed reality - icra 2022 accompanying video
-
 21:34
21:34
tornado: automatic generation of probing-secure masked bitsliced implementations
-
 49:48
49:48
masking techniques i (ches 2023)
-
 24:51
24:51
an instruction set extension to support software-based masking
-
 43:50
43:50
masking post-quantum cryptography ii (ches 2023)
-
 25:01
25:01
new first-order secure aes performance records
-
 1:29:54
1:29:54
session on leakage resilience and masking verification
-
 19:46
19:46
hardware masking, revisited