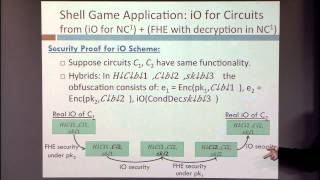
breaking the sub exponential barrier in obfustopia
Published 7 years ago • 156 plays • Length 23:38Download video MP4
Download video MP3
Similar videos
-
 22:07
22:07
patchable indistinguishability obfuscation io for evolving software
-
 1:04:37
1:04:37
015 fhe based on the ntru problem: challenges and new constructions w/ hilder vitor lima pereira
-
 17:21
17:21
indistinguishability obfuscation and uces: the case of computationally unpredictable sources
-
 2:50
2:50
indistinguishability obfuscation for all circuits from secret key functional encryption
-
 31:02
31:02
indistinguishability obfuscation from simple-to-state hard problems: new assumptions, new techn...
-
 46:38
46:38
breaking the classification barrier
-
 1:40:39
1:40:39
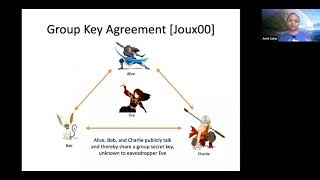
amit sahai | indistinguishability obfuscation: how to hide secrets within software
-
 3:15:39
3:15:39
indistinguishability obfuscation tutorial
-
 1:11:36
1:11:36
applications of obfuscation i
-
 1:15
1:15
chapter 6 - exploiting software vulnerabilities
-
 1:04:00
1:04:00
tutorial on obfuscation
-
 27:36
27:36
indistinguishability obfuscation for turing machines with unbounded memory
-
 52:00
52:00
indistinguishability obfuscation via mathematical proofs of equivalence
-
 31:04
31:04
how to construct indistinguishability obfuscation from compact functional encryption
-
 43:40
43:40
obfuscation iii
-
 19:03
19:03
cryptanalysis of a theorem decomposing the only known solution to the big apn problem
-
 33:01
33:01
substructuring, integration methods and simulation errors
-
 1:04:00
1:04:00
indistinguishability obfuscation and learning problems
-
 1:24:58
1:24:58
indistinguishability obfuscation from simple-to-state hard problems
-
 38:20
38:20
recent advances on foundations of program obfuscation
-
 1:15
1:15
chapter 6 - exploiting software vulnerabilities
-
 40:19
40:19
nov live | structures and subsea composites with simon eves