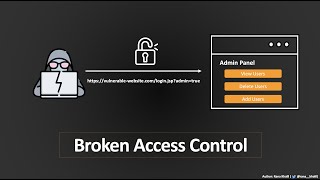
broken access control vulnerabilities | firstblood v1 | bug bounty service
Published 1 year ago • 2K plays • Length 5:38Download video MP4
Download video MP3
Similar videos
-
 6:20
6:20
broken session management | firstblood v1 | bug bounty service
-
 2:44
2:44
account override vulnerability | firstblood v1 | bug bounty service
-
 4:54
4:54
parameter stuffing vulnerability | firstblood v1 | bug bounty service
-
 1:25
1:25
what are access control vulnerabilities | owasp top 10 | bug bounty service llc
-
 8:07
8:07
application / business logic vulnerability | firstblood v1 | bug bounty service 5 business logic
-
 5:42
5:42
information disclosure vulnerability | firstblood v1 | bug bounty service
-
 4:57
4:57
html source code analysis to broken access control | fastfoodhackings | bug bounty service
-
 9:34
9:34
05- vulnerabilities - insecure direct object reference (idor)
-
 3:27
3:27
$15,000 bounty : remote code execution via file upload vulnerability | poc | bug bounty 2023
-
 9:58
9:58
broken b-f protection, ip block | web security academy | portswigger labs
-
 3:21
3:21
business logic vulnerability with hidden input | firstblood v3 | bug bounty service
-
 2:53
2:53
what are cross-origin resource sharing (cors) vulnerabilities | owasp top 10 | bug bounty service
-
 1:34
1:34
$500 bounty for improper access control | bug bounty 2023
-
 1:46
1:46
access control vulnerability | bug bounty poc | lazy pentester
-
 6:10
6:10
tips and tricks: broken access control (bug bounty approach)
-
 39:33
39:33
broken access control | complete guide
-
 5:01
5:01
idor and xss vulnerability | fastfoodhackings | bug bounty service
-
 1:37
1:37
$900 bounty for improper access control-generic vulnerability | bug bounty