bytes check point best practice highlight 1 - threat emulation
Published 10 years ago • 148 plays • Length 2:16Download video MP4
Download video MP3
Similar videos
-
 4:07
4:07
bytes check point best practice - highlight - avoiding endpoint disasters
-
 1:46
1:46
check point threat emulation
-
 2:57
2:57
check point best practices - highlight - virtual systems
-
 1:42
1:42
bytes check point best practice - key discussion - mobile enterprise client
-
 48:25
48:25
bytes webinar - exclusive review of r77 & threat emulation from check point
-
 26:34
26:34
introduction to cyber threat intelligence | tryhackme
-
 24:47
24:47
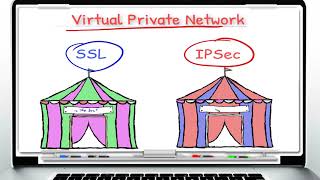
introduction to check point ssl vpn vs ipsec vpn part1
-
 28:46
28:46
understanding check point corexl part 1
-
 48:25
48:25
bytes webinar exclusive review of r77 & threat emulation from check point
-
 4:49
4:49
bytes check point best practice seminars - key demo - mobile security
-
 3:59
3:59
check point threat emulation
-
 3:59
3:59
sandblast agent anti-bot protects the endpoint from bot invasions | tech bytes
-
 3:05
3:05
check point jump start: smb appliance security – 14-threat emulation and sandboxing
-
 6:33
6:33
check point demo days v1 1 network stage 2 0 experiencing threat emulation and practical pre
-
 3:59
3:59
threat emulation explained by check point | advanced threat prevention
-
 5:33
5:33
bytes cyber consulting - introduction to penetration testing