cannot access memory at address // debugging pie binaries affected by aslr - bin 0x2e
Published 4 years ago • 41K plays • Length 13:22Download video MP4
Download video MP3
Similar videos
-
 3:20
3:20
contoh cara bypass address space layout randomization (aslr) di target linux oleh kurniawan
-
 19:57
19:57
pwn.college - memory errors - aslr
-
 14:35
14:35
ret2plt to bypass nx and aslr in linux x64
-
 3:49
3:49
aslr
-
 44:14
44:14
34c3 - aslr on the line
-
 9:54
9:54
#10 - rop emporium 7: ret2csu
-
 12:17
12:17
buffer overflow on a modern system impossible? stack0: part 1 - bin 0x21
-
 11:58
11:58
understanding aslr and its bypass || binary exploitation - 0xb
-
 19:45
19:45
03 bypass aslr - #method 1 (jmp esp)
-
 6:29
6:29
bypassing the linux kernel aslr and exploiting a buffer overflow vulnerable application with ret2esp
-
 8:25
8:25
bufferoverflow linux with aslr enabled
-
 13:35
13:35
reversing statically-linked binaries with function signatures - bin 0x2d
-
 56:33
56:33
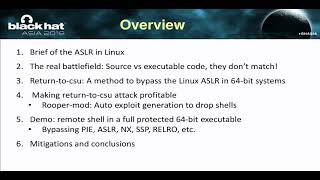
return-to-csu: a new method to bypass 64-bit linux aslr