code protection
Published 8 years ago • 1K plays • Length 2:23Download video MP4
Download video MP3
Similar videos
-
 3:19
3:19
untrusted user code isolation
-
 3:45
3:45
os isolation from application code part 1
-
 1:31
1:31
password protecting a resource
-
 1:12
1:12
mandatory code signing
-
 0:49
0:49
passcodes and touch id
-
 3:28
3:28
os and resource protection
-
 2:36
2:36
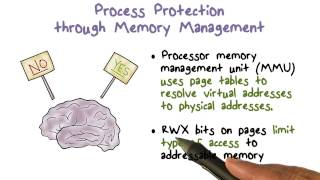
process protection through memory management
-
 2:44
2:44
preventing malicious code execution
-
 25:46
25:46
lift and why it rocks, part 2 code
-
 48:48
48:48
20 emerging technologies that will change the world
-
 57:19
57:19
meta interview question | system design: coding contest platform
-
![[ grunsec ] keep your code safe during the development path using opensource tools](https://i.ytimg.com/vi/MF32O89tuKA/mqdefault.jpg) 41:07
41:07
[ grunsec ] keep your code safe during the development path using opensource tools
-
 1:29
1:29
complete mediation the user code
-
 3:19
3:19
data protection
-
 3:44
3:44
security review & audit - design, architecture and code review
-
 1:05
1:05
code signing
-
 29:22
29:22
usenix security '17 - syntia: synthesizing the semantics of obfuscated code
-
 31:48
31:48
code security reinvented: navigating the era of ai - joseph katsioloudes, github
-
 3:09
3:09
os isolation from application code part 2