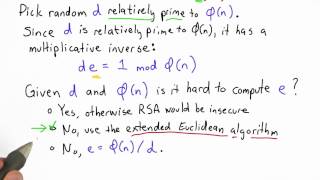
computing d still hard - applied cryptography
Published 12 years ago • 686 plays • Length 1:19Download video MP4
Download video MP3
Similar videos
-
 3:27
3:27
factoring is still hard - applied cryptography
-
 0:19
0:19
compute d - applied cryptography
-
 0:50
0:50
compute e - applied cryptography
-
 0:41
0:41
compute d solution - applied cryptography
-
 5:32
5:32
deep neural network hardware accelerator on fpga
-
 6:45
6:45
symmetric key and public key encryption
-
 1:10:02
1:10:02
lecture 24: man-in-the-middle attack, certificates and pki by christof paar
-
 0:29
0:29
picking e and d - applied cryptography
-
 1:15
1:15
one way function - applied cryptography
-
 1:54
1:54
totient and factoring - applied cryptography
-
 1:26
1:26
secure computation - applied cryptography
-
 0:23
0:23
useful certificates - applied cryptography
-
 3:27
3:27
cut and choose - applied cryptography
-
 0:44
0:44
wire labels solution - applied cryptography
-
 1:13
1:13
back to signatures - applied cryptography
-
 2:33
2:33
ssh authentication in practice - applied cryptography
-
 0:13
0:13
compute e solution - applied cryptography
-
 2:06
2:06
summary - applied cryptography
-
 0:15
0:15
optional: complexity - applied cryptography