cyber security access models ( dac, mac, rbac and abac ) - arabic
Published 1 year ago • 3.9K plays • Length 11:47
Download video MP4
Download video MP3
Similar videos
-
 7:39
7:39
role-based access control (rbac) vs. attribute-based access control (abac)
-
 20:39
20:39
explain access control models| discretionary dac, mandatory mac, rbac, rule, attribute, risk based
-
 2:35
2:35
mandatory access control (mac) models
-
 20:39
20:39
cyber security day 14 data access controls dac mac rbac abac comptia security
-
 12:31
12:31
access control models (dac, non-dac, ibac, rbac, rubac, tbac, abac, mac, lbac)
-
 1:12
1:12
discretionary access control
-
 3:03
3:03
rbac vs abac | identity & access management | iam
-
 14:55
14:55
6 x access control models (rbac, rubac, mac, dac, abac, risk bac)
-
 3:07
3:07
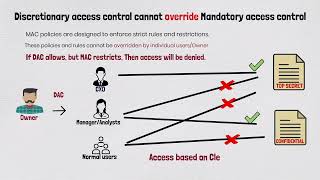
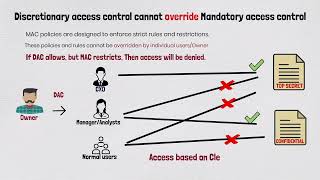
access control models: why discretionary access control cannot override mandatory access control?
-
 4:45
4:45
access controls: mandatory, discretionary and role-based (dac, mac and rbac)
-
 27:13
27:13
cybersecurity - access control models by arash deljoo
-
 14:01
14:01
authentication & authorization explained: master rbac & abac techniques for secure access control
-
 5:48
5:48
access control models: an overview of the four main types
-
 4:06
4:06
mandatory access controls (mac), bell-lapadula, and biba explained.
-
 8:00
8:00
role-based access control (rbac) explained: how it works and when to use it
-
 31:43
31:43
unit - 8 - lecture 2 dac - mac and rbac security models
-
 2:55
2:55
what is mandatory access control (mac)?
Clip.africa.com - Privacy-policy
 7:39
7:39
 20:39
20:39
 2:35
2:35
 20:39
20:39
 12:31
12:31
 1:12
1:12
 3:03
3:03
 14:55
14:55
 3:07
3:07
 4:45
4:45
 27:13
27:13
 14:01
14:01
 5:48
5:48
 4:06
4:06
 8:00
8:00
 31:43
31:43
 2:55
2:55