databases: what is the best way to store ssh fingerprints and public keys?
Published 2 years ago • 6 plays • Length 2:14Download video MP4
Download video MP3
Similar videos
-
 5:39
5:39
why doing ssh with key pairs is better than passwords
-
 4:36
4:36
what is a ssh key fingerprint and how is it generated? (5 solutions!!)
-
 21:29
21:29
how to use multiple ssh keys | managing different ssh keys on your system
-
 10:12
10:12
ssh keys
-
 6:30
6:30
generate ssh keys for windows - secure shell easy way
-
 15:12
15:12
the absolute best intro to monads for software engineers
-
 8:54
8:54
how ssh works
-
 6:27
6:27
putty ssh private public key windows and linux with puttygen
-
 1:49
1:49
connect using ssh by key fingerprint (2 solutions!!)
-
 3:03
3:03
how to get asked for ssh key passphrase once and only when needed? (3 solutions!!)
-
 1:34
1:34
what is the best way to backup an ssh key in case my hard drive fails, etc?
-
 3:10
3:10
get the fingerprint of an existing ssh public key (3 solutions!!)
-
 1:22
1:22
are there security problems with storing public ssh keys in a database?
-
 1:11
1:11
what s the best way to migrate ssh keys and certs from one mac to another?
-
 2:28
2:28
what is the priority between ssh key types on a ssh connection? (2 solutions!!)
-
 10:16
10:16
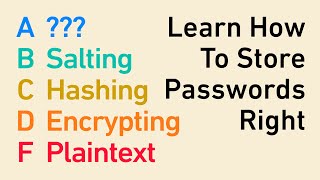
password storage tier list: encryption, hashing, salting, bcrypt, and beyond
-
 1:42
1:42
ssh key fingerprints don't match
-
 1:23
1:23
is it possible to have multiple ssh keys?
-
 12:13
12:13
add ssh key to vps server linux server ssh setup #cloud #security
-
 18:46
18:46
ssh key authentication | how to create ssh key pairs
-
 1:36
1:36
how to tell if a public ssh key has a passphrase? (2 solutions!!)
-
 1:21
1:21
software engineering: security pattern to store ssh keys