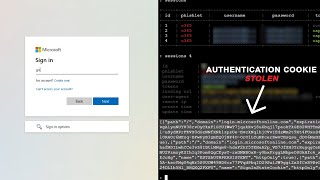
do this to avoid mfa compromise & attacks
Published 2 years ago • 454 plays • Length 1:38Download video MP4
Download video MP3
Similar videos
-
 4:48
4:48
how to use mfa | what to do if i receive an unexpected mfa request?
-
 3:00
3:00
what is mfa? and why you need it.
-
 0:29
0:29
what do you do when you get mfa prompts you didn't request?
-
 1:21
1:21
cybersecurity 101: how to avoid mfa bombing, fatigue, and attacks | uber and the multi-factor push
-
 10:16
10:16
hacking two factor authentication: four methods for bypassing 2fa and mfa
-
 3:58
3:58
attacker in the middle - how mfa is bypassed
-
 5:05
5:05
stop using this two-factor authentication (2fa) method!
-
 6:55
6:55
stop using google authenticator❗(here's why secure 2fa alternatives)
-
 12:47
12:47
hackers bypass google two-factor authentication (2fa) sms
-
 29:39
29:39
setting up and using evilginx 3.0 #phishing #evilginx #cybersecurity
-
 2:08:55
2:08:55
comptia a certification. crash course for core 2
-
 24:24
24:24
turn on mfa: real-world examples to avoid fraud and mayhem
-
 3:55
3:55
mfa fatigue attacks - how mfa is bypassed
-
 9:22
9:22
mfa can be easily bypassed - here's how
-
 1:07
1:07
mfa attacks: push notification fatigue demonstration
-
 5:29
5:29
does mfa stop 99% of attacks? - cybersecurity mythbusters
-
 3:21
3:21
protect your users from mfa fatigue
-
 8:13
8:13
is mfa still safe? | how hackers bypass mfa
-
 4:32
4:32
how arctic wolf disrupts business email compromise attacks
-
 3:46
3:46
dfars compliance: a contractors guide to mfa
-
 51:00
51:00
breaking password dependencies: challenges in the final mile at microsoft
-
 2:16
2:16
what is multi-factor authentication fatigue attack? | explained