dr.r.suganya|unauthorized access|sns institutions
Published 9 days ago • 13 plays • Length 5:03Download video MP4
Download video MP3
Similar videos
-
 8:22
8:22
dr.r.suganya|evidence collection & data seizure|sns institution
-
 6:17
6:17
dr.r.suganya|malware infection|sns institutions
-
 8:42
8:42
dr.r.suganya|key management|sns institutions
-
 8:10
8:10
dr.r.suganya|public key cryptography and rsa|sns institutions
-
 29:38
29:38
secure your cloud infrastructure with kubernetes security posture management (kspm)
-
 52:00
52:00
a cloud security architecture workshop
-
 46:58
46:58
software defined networking and network security
-
 8:59
8:59
dr.r.suganya|digital signature|sns institutions
-
 6:02
6:02
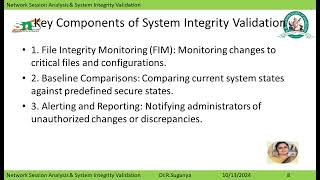
dr.r.suganya|network session analysis, system integrity validation|sns institutions
-
 22:50
22:50
security as a service - cloud computing - cloud computing and services
-
 4:42
4:42
sdn-based cyber security
-
 5:43
5:43
dr.s.dhivya/assistant professor/department of commerce ca/drsnsrcas/lecture -levy and collection tax
-
 8:18
8:18
aws security assessment
-
 5:55
5:55
cloud computing tutorial - aws security design principles
-
 3:01
3:01
getting started with cloud security
-
 0:18
0:18
security solutions in healthcare
-
 1:36
1:36
secure the software supply chain and ensure regulatory compliance with endor labs on google cloud
-
 8:34
8:34
a.s.arul sowmiya ap/aids | origins of cloud computing | sns institutions
-
 6:59
6:59
a.s.arul sowmiya ap/aids | cloud scenarios | sns institutions