equifax then, log4j now – reveal and seal off attack paths with deepfence
Published 2 years ago • 113 plays • Length 52:17Download video MP4
Download video MP3
Similar videos
-
 11:19
11:19
the log4j vulnerability: patching and mitigation
-
 15:41
15:41
apache log4j: the exploit that almost killed the internet
-
 22:41
22:41
the log4j vulnerability exploit explained
-
 12:05
12:05
log4j 2.15 vs 2.17 | how to update log4j latest version? log4j 2.17 #log4jvulnerability #dos
-
 20:50
20:50
log4j vulnerability (log4shell) explained - for java developers
-
 7:21
7:21
how bad is log4j and what we should do!
-
 26:31
26:31
log4j & jndi exploit: why so bad? - computerphile
-
 49:17
49:17
the real story of hitler in argentina...
-
 18:47
18:47
logjam attack - computerphile
-
 8:52
8:52
critical vulnerability in java log4j affecting unifi, apple, minecraft, and many others!
-
 0:59
0:59
how does the log4j cve work?
-
 15:08
15:08
apache log4j vulnerability explained
-
 0:30
0:30
attack diagram shows one way to detect log4j with extrahop
-
 5:01
5:01
log4j: the software ‘used across the entire internet’ that’s now vulnerable
-
 0:55
0:55
what is the log4j vulnerability? #shorts
-
 15:04
15:04
logs on fire? | log4j vulnerability | how to remediate them asap? | tech primers
-
 8:42
8:42
how hackers exploit log4j to get a reverse shell (ghidra log4shell demo) | hakbyte
-
 9:08
9:08
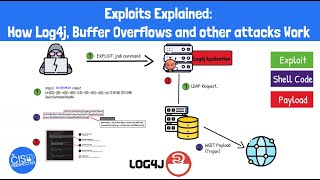
exploits explained: how log4j, buffer overflows and other exploits work
-
 1:18
1:18
how to respond to log4j vulnerability
-
 5:24
5:24
apache log4j dpa security update - cve-2021-44228
-
 2:00
2:00
log4j | why your scanners can't find it
-
 0:39
0:39
what is apache log4j?