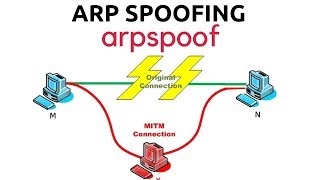
ethical hacking #29 : theory behind arp spoofing
Published 5 years ago • 65 plays • Length 5:05Download video MP4
Download video MP3
Similar videos
-
 13:46
13:46
ethical hacking #31 : coding arp spoofer
-
 1:32
1:32
arp spoofing attack explained
-
 6:53
6:53
get usernames and passwords with ettercap, arp poisoning (cybersecurity)
-
 10:02
10:02
arp spoofing with arpspoof - mitm
-
 3:46
3:46
remote code execution (rec) | cve-2024-7945 | poc
-
 5:01
5:01
every cyber attack type explained in 5 minutes
-
 25:48
25:48
malware analysis | asyncrat injector | aes decryption with cyberchef, and iso file forensics
-
 12:00
12:00
ethical hacking beginners tutorial 20 man in the middle attack arp spoofing live demo 720p 30fp
-
 11:35
11:35
arp poisoning | man-in-the-middle attack
-
 8:18
8:18
mitm attack | arp spoofing | arp poisoning in kali linux
-
 8:19
8:19
ethical hacking #32 : forwarding packets and restoring arp tables
-
 19:40
19:40
ethical hacking #30 : crafting malicious arp packet
-
 9:00
9:00
ethical hacking - part-9.3 - wireshark, arp spoofing
-
 11:30
11:30
bettercap arp spoofing🕵🏼man in the middle - mitm 15.2
-
 16:46
16:46
arp poisoning or arp spoofing attack - explanation & demonstration