extending the zero trust security model for containerized applications to public clouds
Published 5 years ago • 450 plays • Length 46:38Download video MP4
Download video MP3
Similar videos
-
 3:43
3:43
zero trust explained in 4 mins
-
 2:20
2:20
active zero trust security for containers and kubernetes
-
 31:55
31:55
zero trust architecture for containers with kata and confidential computing
-
 8:57
8:57
zero trust security implementation - essentials series - episode 1
-
 19:25
19:25
zero trust for ot
-
 7:44
7:44
what is zero trust network access (ztna)? the zero trust model, framework and technologies explained
-
 55:42
55:42
webinar: zero trust security for cloud native apps
-
 28:23
28:23
evolve to zero trust security model with anthos security
-
 37:45
37:45
implementing zero trust architecture: a step-by-step guide part 1
-
 36:10
36:10
lisa16 - zero trust networks: building systems in untrusted networks
-
 45:42
45:42
overview of zero trust architectures
-
 4:07
4:07
secure zero trust access for kubernetes
-
 57:35
57:35
extending rubrik zero trust data security to your aws environments
-
 16:10
16:10
full-stack security chain of trust and best practices in cloud
-
 1:02:19
1:02:19
zero-trust security for kubernetes and container workloads
-
 23:34
23:34
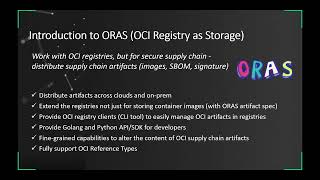
secure container supply chain with notation, oras, and ratify
-
 21:04
21:04
operate with zero trust using beyondcorp enterprise
-
 15:15
15:15
what's new in zero trust
-
 1:27
1:27
zero trust security for manufacturing
-
 25:58
25:58
5g and zero trust for maximum security
-
 21:08
21:08
demo: suse’s neuvector, zero trust security for containers
-
 1:02
1:02
is zero trust the solution to securing a multi-cloud world?