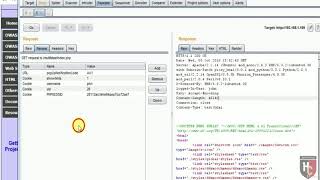
forceful browsing via session variables
Published 8 years ago • 1.1K plays • Length 11:13Download video MP4
Download video MP3
Similar videos
-
 9:25
9:25
web application penetration testing | forced browsing with burp suite
-
 4:39
4:39
forced browsing | vulnerability video training
-
 3:23
3:23
11.3 how to hack cookies and sessions manipulation
-
 9:12
9:12
finding xss vulnerabilities with burp
-
 2:19:33
2:19:33
apis for beginners - how to use an api (full course / tutorial)
-
 3:38
3:38
session fixation attack - security testing | session management vulnerabilities
-
 7:43
7:43
burpsuite - intercept https request
-
 4:39
4:39
06.using burp suite comparer tool for analyzing varied server responses | step-by-step guide
-
 10:53
10:53
taking over https traffic with bettercap using sslstrip and explaining hstshijack - testing mitm
-
 2:09
2:09
session fixation attack
-
 14:55
14:55
php sessions & cookies - output buffering - headers already sent warning - full php 8 tutorial
-
 7:20
7:20
securely storing php configuration settings
-
 5:24
5:24
php tutorial for beginners 27 # how to unset or destroy php sessions
-
 5:04
5:04
forced choices
-
 5:17
5:17
solved: how to configure burp suite to work with https! (avoid https warnings in burp suite)
-
 1:24
1:24
are querystring parameters secure in https (http ssl)?
-
 9:47
9:47
day 194 || aws cloudfront tutorial || default cache behavior - restrict viewer access
-
 34:31
34:31
web app pentesting - http cookies & sessions