forensic analysis of a rootkit with sysdig inspect
Published 6 years ago • 1.9K plays • Length 1:02Download video MP4
Download video MP3
Similar videos
-
 3:59
3:59
container forensics analysis and postmortem
-
 1:11
1:11
sysdig inspect overview
-
 3:38
3:38
sysdig monitor container troubleshooting and forensics
-
 2:45
2:45
rootkits - sy0-601 comptia security : 1.2
-
 2:19
2:19
the rootkit paradox
-
 8:57
8:57
how to tell if your pc is hacked? process forensics
-
 2:59
2:59
how to detect a rootkit through memory analysis - stuxnet
-
 6:38
6:38
what is a rootkit - definition, prevention, types
-
![3 signs to check if your computer's hacked [spy software]](https://i.ytimg.com/vi/g_E_kzTlAA4/mqdefault.jpg) 5:34
5:34
3 signs to check if your computer's hacked [spy software]
-
 10:19
10:19
how to know if your pc is hacked? suspicious network activity 101
-
 3:40
3:40
how to tell if your windows 10 or 11 computer has been hacked
-
 25:21
25:21
live system analysis - part 2: computer security lectures 2014/15 s1
-
 10:33
10:33
beyond openshift monitoring and security: troubleshooting and forensics with sysdig
-
 2:07
2:07
sysdig falco - open source docker security - detecting a write attack below/bin
-
 3:45
3:45
rootkit detection and removal
-
 13:36
13:36
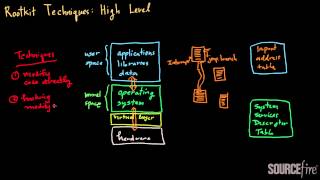
rootkits (part 2): high-level techniques
-
 2:15
2:15
rootkit vs. bootkit - what is the difference between a rootkit and bootkit?
-
 40:01
40:01
sysdig technical deep dive: from wireshark to sysdig
-
 5:37
5:37
rootkits as fast as possible
-
 20:02
20:02
runtime security and forensics with sysdig secure on kubernetes
-
 4:06
4:06
kubernetes and container topology mapping
-
 25:03
25:03
incident response and computer forensics on rootkits