getting executables into memory (going fileless)
Published 1 year ago • 2.3K plays • Length 12:51Download video MP4
Download video MP3
Similar videos
-
 7:22
7:22
fileless ransomware: powershell netwalker
-
 20:45
20:45
fileless malware and apt defense
-
 3:09
3:09
fileless malware attacks in cyber security
-
 2:31
2:31
what is a fileless attack?
-
 13:45
13:45
cybersecurity insights - fileless attacks
-
 18:53
18:53
jonathan blow on backdoors and cybersecurity
-
 2:56
2:56
watch this russian hacker break into our computer in minutes | cnbc
-
 45:45
45:45
keynote: cobalt strike threat hunting | chad tilbury
-
 9:50
9:50
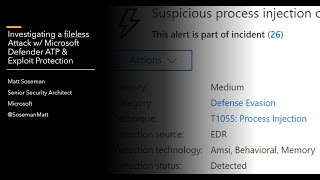
investigating a fileless attack w/ microsoft defender atp & exploit protection
-
 9:39
9:39
ransomware attack simulation
-
 0:44
0:44
how to detect and mitigate fileless malware attacks with microsoft sentinel
-
 17:51
17:51
extract shellcode from fileless malware like a pro
-
 1:19
1:19
malware minute: analyzing a powershell attack
-
 32:00
32:00
investigating a malicious stealer to learn detect-it-easy!
-
 5:04
5:04
what is fileless malware? : simply explained
-
 20:42
20:42
fileless malware: how it works
-
 2:56
2:56
eset cybersecurity tips & tricks: fileless malware attacks
-
 2:05
2:05
5 things you should know about fileless malware attacks
-
 2:48
2:48
fileless threat detection
-
 9:26
9:26
fileless malware #cybersecurity #2024 #ethicalhacking #trending
-
 9:48
9:48
bypassing a fully patched windows 11 defender with a meterpreter shell using scarecrow!
-
 55:29
55:29
unit 0.2 malicious code and application attacks (cissp ch 21)