hacking and securing json web tokens(jwt) - course introduction
Published 4 years ago • 459 plays • Length 2:41Download video MP4
Download video MP3
Similar videos
-
 4:42
4:42
hacking and securing json web tokens(jwt) - none signature attack
-
 7:09
7:09
hacking and securing json web tokens(jwt) - manually creating hs256 signature
-
 6:30
6:30
json web token hacking
-
 2:18
2:18
session vs token authentication in 100 seconds
-
 14:53
14:53
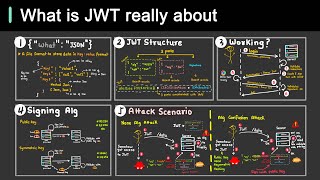
what is jwt and why should you use jwt
-
 14:34
14:34
cracking json web tokens
-
 13:15
13:15
how hackers hack json web tokens
-
 27:52
27:52
the hacker's guide to jwt security
-
 6:37
6:37
hacker tools - jwt_tool
-
 18:28
18:28
attacking jwt - header injections
-
 12:20
12:20
bug bounty explained! how hackers break into your website using only json?! protect your website!
-
 0:32
0:32
authentication and authorization using jwt token and roles-based access control
-
 0:57
0:57
day 27: json web tokens (jwt) | #cybersecurityawarenessmonth 2023
-
 35:24
35:24
jwt hacking (json web token)
-
 5:14
5:14
why is jwt popular?
-
 0:28
0:28
authentication vs authorization #shorts
-
 46:46
46:46
json web tokens crash course - jwt tokens explained
-
 1:00
1:00
how to use a jwt token to get data from an api with javascript
-
 1:00
1:00
don’t use jwt for login sessions
-
 1:07
1:07
how does jwt work