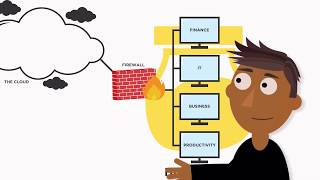
honeypots in cyber security **explained**
Published 3 years ago • 15K plays • Length 8:33Download video MP4
Download video MP3
Similar videos
-
 2:35
2:35
what is a honeypot (cybersecurity)? honeypot benefits and risks
-
 1:13
1:13
what is a honeypot?
-
 4:08
4:08
honeypots & honeynets
-
 34:26
34:26
honeypot introduction (cyber security series)
-
 2:21
2:21
what is a honeypot - cyber security tutorial
-
 35:57
35:57
honeypots
-
 6:56
6:56
what is a honeypot? : simply explained!
-
 10:52
10:52
what are honeypots, and how to avoid them.
-
 12:07
12:07
the top 3 uses for a raspberry pi!!
-
 14:42
14:42
it took just 12 seconds - catching hackers with a honey pot!
-
 2:49
2:49
hacker demonstrates security risks of free public wi-fi
-
 7:07
7:07
what is cyber security | how it works? | cyber security in 7 minutes | cyber security | simplilearn
-
 2:18
2:18
honeypot | what is honeypot in simple words?
-
 0:28
0:28
what is a honeypot in cybersecurity? | cybersec lingo | ivacy vpn
-
 2:08
2:08
081 honeypots and honeynets
-
 1:21
1:21
honeypots
-
 12:21
12:21
cybersecurity 101 - what is a honeypot
-
 3:40
3:40
what are honeypots? network security
-
 2:58
2:58
what are honeypots and honeytokens? explained
-
 49:10
49:10
tech201 honeypots for active defense a practical guide to deploying honeynets within the enterprise
-
 1:30
1:30
honeypots classification
-
 2:14
2:14
honeypot deployment