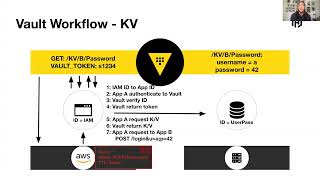
how do developers, operations, and security typically use vault?
Published 5 years ago • 667 plays • Length 3:11Download video MP4
Download video MP3
Similar videos
-
 3:39
3:39
hashicorp vault explained in 180 seconds
-
 16:53
16:53
introduction to hashicorp vault with armon dadgar
-
 22:32
22:32
hashicorp vault and getting day 2 operations right
-
 36:33
36:33
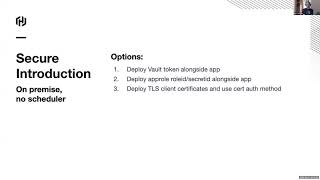
think like a vault developer: secure introduction at scale
-
 58:12
58:12
vault 1.12 overview
-
 20:19
20:19
introduction to hashicorp vault
-
 23:45
23:45
vault and active directory
-
 58:18
58:18
vault 1.11 overview
-
 17:16
17:16
keeping a secret with hashicorp vault
-
 11:43
11:43
how to use vault secrets operator in kubernetes
-
 44:25
44:25
how hashicorp vault solves the top 3 cloud security challenges
-
 22:55
22:55
the 4 primary vault use cases
-
 0:53
0:53
run a hashicorp 🔥 vault instance 🔥 in less than a minute - security and secret management
-
 58:05
58:05
hashicorp vault and venafi: speed and security for cloud operating model success
-
 29:16
29:16
zero trust security with boundary and vault
-
 22:56
22:56
hashicorp vault - what is vault, overview, use cases & architecture explained
-
 55:23
55:23
webinar: build a secure cloud with aws and hashicorp vault
-
 24:38
24:38
building a privileged account management system with vault
-
 30:33
30:33
security and fundamentals at scale with vault
-
 25:09
25:09
security keynote: zero trust architecture - a more secure world with vault, boundary, and consul
-
 21:49
21:49
introduction to hashicorp vault on kubernetes for beginners