how do hashing algorithms like sha and md5 secure digital data?
Published 10 months ago • 2 plays • Length 0:56Download video MP4
Download video MP3
Similar videos
-
 0:57
0:57
how do hashing algorithms like sha and md5 ensure data security?
-
 12:36
12:36
md5 algorithm | what is md5 algorithm? | md5 algorithm explained | network security | simplilearn
-
 12:36
12:36
hashing and hash cracking explained simply! (2021) | md5, sha1, and sha256
-
 11:42
11:42
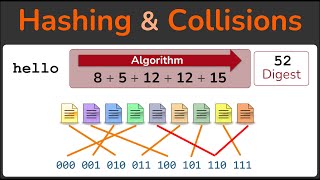
hashing, hashing algorithms, and collisions - cryptography - practical tls
-
 0:53
0:53
how do hashing algorithms like md5, sha1 & sha256 work?
-
 49:40
49:40
top hashing algorithms in cryptography | md5 and sha 256 algorithms explained | simplilearn
-
 8:12
8:12
hashing algorithms and security - computerphile
-
 10:21
10:21
sha: secure hashing algorithm - computerphile
-
 10:27
10:27
python md5 implementation
-
 14:00
14:00
how the md5 hash function works (from scratch)
-
 15:59
15:59
hashcat tutorial for beginners || sha,md5,bcrypt & salted hash ||exercise also ||
-
 9:45
9:45
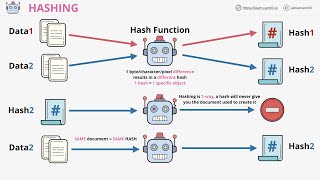
what is hashing? | what is hashing with example | hashing explained simply | simplilearn
-
 10:12
10:12
#34 md5 algorithm ( message digest 5) working and example |cns|
-
 12:17
12:17
intro to hashing | sha1, sha2 and sha256, md5, hash tables, digitally signing
-
 0:54
0:54
how can i understand basic hashing techniques like sha and md5?
-
 5:34
5:34
#38 sha ( secure hash algorithm )algorithm with example |cns|
-
 3:32
3:32
what are hash values? important hash value algorithms md5, sha-1 and sha 2 - networkers home
-
 7:42
7:42
hashing | sha-1(secure hashing algorithm) | comparison with md-5 | working | theory | numerical
-
 56:32
56:32
new approaches for building cryptographic hash functions
-
 13:20
13:20
hashing - what it is, how it's used and why it matters - with md5 and sha2-256 examples
-
 2:13
2:13
secure hashing algorithm (sha)
-
 0:59
0:59
how does hashing work in digital security with sha and md5?