how forensic investigators find passwords using memory forensics (otter ctf) with volatility
Published 2 years ago • 2K plays • Length 12:55Download video MP4
Download video MP3
Similar videos
-
 32:00
32:00
introduction to memory forensics with volatility 3
-
![lsadump: dumping passwords w/ volatility [01] otterctf](https://i.ytimg.com/vi/7iU40hv7HlI/mqdefault.jpg) 7:23
7:23
lsadump: dumping passwords w/ volatility [01] otterctf
-
 14:29
14:29
is your pc hacked? ram forensics with volatility
-
 10:46
10:46
how to get windows information from ram dump using volatility 3? windows username and password!!!
-
 12:33
12:33
extracting information from ram? memory dump analysis with volatility (digital forensics- thm)
-
 7:37
7:37
how to recover encrypted files using photorec
-
 4:56
4:56
how to find financial fraud | uncover fraud
-
 6:21
6:21
✅ how to find hidden recording devices that are not transmitting
-
 23:24
23:24
introduction to memory forensics
-
![export [easy]: hackthebox forensics challenge (volatility - memory dump recovery)](https://i.ytimg.com/vi/ONPumkqjarM/mqdefault.jpg) 18:15
18:15
export [easy]: hackthebox forensics challenge (volatility - memory dump recovery)
-
 13:00
13:00
intro to memory forensics || digital forensics
-
 9:00
9:00
forensics: what data can you find in ram?
-
 27:48
27:48
memory forensics: how to install volatility 3 (and use some of it's plugins)
-
 38:25
38:25
basics of memory forensics - volatility (part 1)
-
 13:12
13:12
digital forensic memory analysis - volatility
-
 40:00
40:00
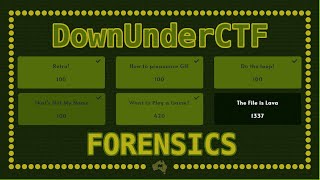
forensics challenge walkthroughs - downunderctf (ductf) 2021
-
 9:53
9:53
live forensics | how to install volatility 3 on windows 11 windows 10 | symbol tables configuration
-
 9:38
9:38
easiest way to capture memory and disk images for digital forensics
-
 1:59:16
1:59:16
malware hunting with memory forensics