how hackers compromise other users
Published 10 months ago • 104K plays • Length 9:55Download video MP4
Download video MP3
Similar videos
-
 36:41
36:41
how hackers compromise big networks (with netexec)
-
 20:01
20:01
how hackers move through networks (with ligolo)
-
 19:31
19:31
how hackers can bypass your security defenses
-
 15:40
15:40
chinese hackers use visual studio code to target asian governments
-
 19:00
19:00
how hackers use netsh.exe for persistence & code execution (sliver c2)
-
 31:07
31:07
hacking windows trustedinstaller (god mode)
-
 16:38
16:38
detect hackers & malware on your computer (literally for free)
-
 19:19
19:19
the insane world of north korean hackers
-
 9:34
9:34
16yr old hacks webcams at anti-scam call center!
-
 21:24
21:24
stealing computer passwords on login
-
 27:11
27:11
the phishing website that hacked linus tech tips
-
 19:57
19:57
i stole a microsoft 365 account. here's how.
-
 25:57
25:57
how hackers & malware spoof processes
-
 17:49
17:49
a hacker's backdoor: service control manager
-
 20:55
20:55
how hackers hide
-
 25:26
25:26
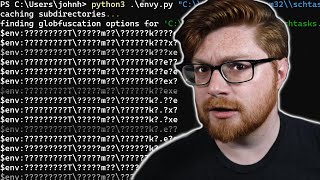
how hackers can hide powershell in environment variables
-
 12:21
12:21
where does malware go on your computer?
-
 41:06
41:06
self-extracting executables for hackers
-
 19:00
19:00
this company got hacked... but how?
-
 12:47
12:47
hackers bypass google two-factor authentication (2fa) sms
-
 22:10
22:10
yet another cybercrime hacking forum...