how relevant are ctfs in real world pentesting and bug hunting
Published 4 years ago • 1.7K plays • Length 4:16Download video MP4
Download video MP3
Similar videos
-
 4:32
4:32
the ugly truth about bug bounty hunting
-
 4:53
4:53
my top paid learning platforms for pentesting and bug hunting
-
 7:01
7:01
why i stopped playing ctfs
-
 2:56
2:56
how to learn coding for pentesting and bug hunting - feat @tcmsecurityacademy
-
 6:44
6:44
why hackers need ctfs | practicing | bug bounty vs ctfs
-
 10:23
10:23
i played hackthebox for 30 days - here's what i learned
-
 5:57
5:57
yeswehack hunter interviews – #8 hakupiku: “bug hunting makes me feel like a detective”
-
 48:11
48:11
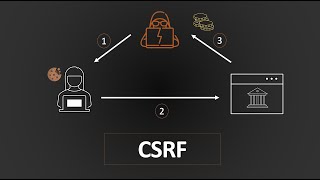
cross-site request forgery (csrf) | complete guide
-
 16:11
16:11
what is the difference between a ctf, hacker training, bugbounty and pentesting?
-
 1:47
1:47
how to be a top bug hunter and cybersecurity professional
-
 1:31
1:31
do ctfs prepare you to be hacker?
-
![from practice labs to real targets - [and no bug bounties]](https://i.ytimg.com/vi/IE0hgOu2q_A/mqdefault.jpg) 1:48
1:48
from practice labs to real targets - [and no bug bounties]
-
 9:08
9:08
pentesting vs. bug bounty vs. pentesting ???
-
 5:59
5:59
the bug hunting methodology - a ready to use formula
-
 5:49
5:49
recon in cybersecurity #1 - bug hunting methodologies and my personal story
-
 38:46
38:46
cissp vs. ceh, cybersecurity degrees, ctfs vs. real-life - cybertalk with hackersploit
-
 4:40
4:40
how to be extremely efficient in cyber and life - the 80-20 principle
-
 4:58
4:58
your first steps in bug bounty hunting - the fast way
-
 13:44
13:44
i played beginner-level security ctfs for 30 days - here's what i learned
-
 10:20
10:20
top 5 ctfs to get started with ethical hacking
-
 2:36
2:36
number one book to get started in bug bounty hunting