how to document identification and authentication controls within your security policies
Published 1 year ago • 32 plays • Length 1:57
Download video MP4
Download video MP3
Similar videos
-
 2:08
2:08
pci requirement 8.4 – document and communicate authentication policies and procedures to all users
-
 3:12
3:12
how to create a physical security policy
-
 2:17
2:17
how to create an access control policy
-
 1:09
1:09
pci requirement 7.3 – document policies & procedures for restricting access to cardholder data
-
 3:09
3:09
how to authenticate documents at trial
-
 33:44
33:44
azure ad app registrations, enterprise apps and service principals
-
 5:15
5:15
understanding identification, authentication, and authorization in security | #informationsecurity
-
 1:09
1:09
pci requirement 8.8 – ensure policies & procedures for authentication are documented
-
 2:00
2:00
pci requirement 8: identify and authenticate access to system components
-
 8:04
8:04
understanding identification, authorization and authentication | free cyber work applied series
-
 0:56
0:56
pci requirement 12.5.1 – establish, document, and distribute security policies and procedures
-
 9:56
9:56
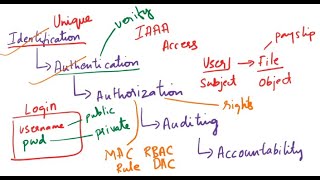
what is identification, authentication, authorization, auditing, accountability| iaaa| cybersecurity
-
 1:51
1:51
iaa (identification, authentication ,authorization and accounting)
-
 1:57
1:57
access and authentication
-
 8:31
8:31
iaaa - identification, authentication, authorization, and accountability (defender course 01.03)
-
 5:42
5:42
document authentication & legalization in canada
-
 4:09
4:09
docusign esignature: how to authenticate and verify recipient identity
-
 12:07
12:07
how to authenticate and legalize your documents/ questions & response
-
 3:52
3:52
explain authentication and authorization - az-900 certification course
-
 3:15
3:15
how to legalize and authenticate your documents for use in vietnam
-
 2:51
2:51
veridos: how can we produce an identity document? find out about the process…
Clip.africa.com - Privacy-policy
 2:08
2:08
 3:12
3:12
 2:17
2:17
 1:09
1:09
 3:09
3:09
 33:44
33:44
 5:15
5:15
 1:09
1:09
 2:00
2:00
 8:04
8:04
 0:56
0:56
 9:56
9:56
 1:51
1:51
 1:57
1:57
 8:31
8:31
 5:42
5:42
 4:09
4:09
 12:07
12:07
 3:52
3:52
 3:15
3:15
 2:51
2:51