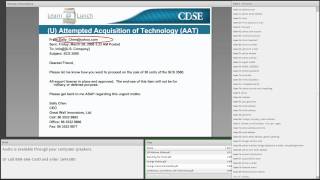
how to spot suspicious behavior, and how to address it
Published 5 years ago • 560 plays • Length 14:59Download video MP4
Download video MP3
Similar videos
-
 4:36
4:36
how to identify a suspicious person
-
 1:35
1:35
suspicious behaviour detection: tracking and analysis enable real-time intervention
-
 6:24
6:24
identifying suspicious activity
-
 5:33
5:33
how to spot manipulated video | the fact checker
-
 8:04
8:04
you're being manipulated and don't even know it | nate pressner | tedxyouth@basel
-
 14:44
14:44
former fbi agent explains how to read body language | tradecraft | wired
-
 9:17
9:17
suspicious activity awareness video: no reservations; suspicious behavior in hotels
-
 25:07
25:07
configure an agentforce service agent | quick start: build your first agent with agentforce
-
 3:02
3:02
4. how to detect physical surveillance with frank smyth
-
![web application pentesting vulnerabilities explained [theory & practical guide]](https://i.ytimg.com/vi/GFb06Ktjdmg/mqdefault.jpg) 51:05
51:05
web application pentesting vulnerabilities explained [theory & practical guide]
-
 8:13
8:13
connections among people: tracking and preventing violence through social network analysis
-
 15:22
15:22
reduce cyber risk with threat exposure management | ceo of picus security explains
-
 0:42
0:42
security awareness training: access to confidential information
-
 8:21
8:21
active surveillance: a new paradigm in patient safety
-
 1:07
1:07
what is suspicious behavior?
-
 1:22
1:22
axis use case inspiration - suspect behavior analysis in cities
-
 33:23
33:23
falcon® exposure management
-
 0:57
0:57
android suspicious photo detection: detect inappropriate images on android via famisafe
-
 30:53
30:53
critical elements of a suspicious contact report
-
 6:29
6:29
it security tutorial - detecting signs of compromise
-
 1:28
1:28
social determinants of health: targets to tackle disparities