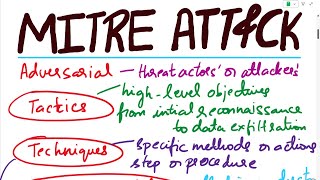
how to use mitre att&ck framework in soc operations | explained by a cyber security professional
Published 11 months ago • 3.2K plays • Length 9:43Download video MP4
Download video MP3
Similar videos
-
 15:28
15:28
how to use mitre att&ck navigator in soc operations with phishing use case explained
-
 4:28
4:28
how mitre att&ck works
-
 30:21
30:21
how to use mitre att&ck framework detailed approach 2022
-
 8:56
8:56
what is mitre att&ck | how can use mitre att&ck framework | cyber kill-chain | rajneesh gupta
-
 7:53
7:53
mitre att&ck framework for beginners
-
 16:43
16:43
mitre attack | mitre att&ck | mitre att&ck explained with an example | mitre att&ck analysis
-
 46:23
46:23
mitre att&ck framework
-
 1:47:11
1:47:11
workshop: mitre att&ck fundamentals
-
 8:59
8:59
mitre att&ck tactics, techniques and mitigations overview : series
-
 2:41
2:41
mitre att&ck explained with phishing email | cyberres sme submission
-
 7:46
7:46
the anatomy of an att&ck
-
 36:34
36:34
what is mitre att&ck? mitre att&ck framework | att&ck tactics and techniques understanding att&ck
-
 5:52
5:52
mitre att&ck framework vs cyber kill-chain | how to use | what is it | rajneesh gupta
-
 6:24
6:24
mitre att&ck framework explained | how to use | cyber kill chain | cybersecurity
-
 9:15
9:15
siem use case & use case framework | explained by cyber security professional
-
 3:09
3:09
what is mitre att&ck framework?
-
 5:21
5:21
mitre att&ck collection techniques demonstrated on cyberbit range
-
 1:19
1:19
mitre's att&ck framework: what is it and how can it help?
-
 3:43
3:43
mitre att&ck® framework
-
 2:52
2:52
how to use the mitre att&ck matrix | free cyber work applied series
-
 30:31
30:31
cyber summit 2020: operationalizing att&ck