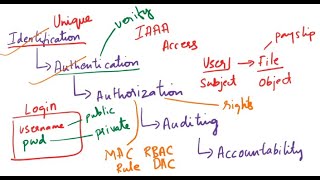
iaaa: identification, authentication, authorization and accountability
Published 5 years ago • 487 plays • Length 7:57
Download video MP4
Download video MP3
Similar videos
-
 8:31
8:31
iaaa - identification, authentication, authorization, and accountability (defender course 01.03)
-
 9:56
9:56
what is identification, authentication, authorization, auditing, accountability| iaaa| cybersecurity
-
 5:29
5:29
iaaa - identification, authentication, authorization and accountability or audit
-
 3:45
3:45
cissp bootcamp: identification authentication authorization and accountability
-
 9:04
9:04
authentication, authorization, and accounting - comptia security sy0-701 - 1.2
-
 2:37
2:37
what is identification, authentication, authorization? | iaa | cybersecurity
-
 48:25
48:25
what is aaa | configure aaa | authentication | authorization | accounting
-
 22:51
22:51
migrate legacy mfa & sspr: authentication methods policy | microsoft entra id
-
 20:33
20:33
configure aaa authentication | cisco ccna 200-301
-
 1:00
1:00
identification authentication authorization accounting and iam
-
 8:52
8:52
certified in cybersecurity | iaaa - part 4
-
 2:18
2:18
cissp identification and authentication, authorization and accountability
-
 1:22
1:22
11 identification vs authentication vs authorization
-
 4:34
4:34
what is aaa (authentication, authorisation, & accounting) & iam? - beginner's cyber security series
-
 1:00
1:00
identification, authentication, authorization, and accountability in iam #shorts #cybersecurity
-
 7:58
7:58
cyber security fundamentals: identification and aaa (cissp & security )
-
 7:57
7:57
iaaa
-
 12:28
12:28
identification and authentication overview.mp4
-
 4:40
4:40
asymmetric encryption - simply explained
Clip.africa.com - Privacy-policy
 8:31
8:31
 9:56
9:56
 5:29
5:29
 3:45
3:45
 9:04
9:04
 2:37
2:37
 48:25
48:25
 22:51
22:51
 20:33
20:33
 1:00
1:00
 8:52
8:52
 2:18
2:18
 1:22
1:22
 4:34
4:34
 1:00
1:00
 7:58
7:58
 7:57
7:57
 12:28
12:28
 4:40
4:40