ibm privileged access management
Published 3 years ago • 323 plays • Length 41:39Download video MP4
Download video MP3
Similar videos
-
 4:20
4:20
why you need privileged account management
-
 2:41
2:41
what is privileged access management? | @solutionsreview explores
-
 5:25
5:25
pam explained. introduction to privileged access management
-
 3:37
3:37
identity & access management (iam)
-
 2:21
2:21
privileged access management (pam) 101
-
 6:11
6:11
protect your business with privileged access management (pam)
-
 4:52
4:52
privileged access management by devolutions - simple pam for it professionals and smbs
-
 51:37
51:37
understanding privileged access management (pam)
-
 1:48
1:48
privileged access manager (pam) end user training | cyberark
-
 31:15
31:15
cybersecurity architecture: who are you? identity and access management
-
 1:05
1:05
identity and access management for ibm i guide
-
 0:31
0:31
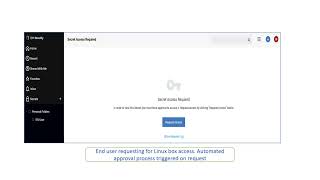
request approval process in ibm security verify privilege vault
-
 0:38
0:38
roles and identity access management
-
 1:39
1:39
privileged access management (pam) with netwrix solutions
-
 5:07
5:07
identity access management (iam) vs privileged access management (pam)
-
 16:31
16:31
beyondtrust endpoint privilege management for windows and mac - demo