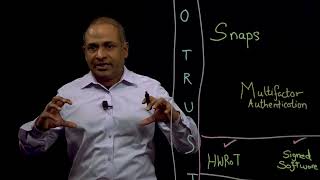
how zero trust security works
Published 1 year ago • 25K plays • Length 4:38Download video MP4
Download video MP3
Similar videos
-
 11:29
11:29
lockheed martin on cyber resiliency, cloud transformation and zero trust | aws verified
-
 3:21
3:21
how convergeone unlocks zero trust with blackberry
-
 32:26
32:26
optimising human hours - best practice for proactive cyber incident management
-
 0:31
0:31
blackberry cybersecurity: disaster averted
-
 3:03
3:03
blackberry prevents: lockbit 2.0 ransomware
-
 4:20
4:20
blackberry prevents h0lygh0st ransomware
-
 3:43
3:43
zero trust explained in 4 mins
-
 0:56
0:56
blackberry | cyber suite zero trust meets zero touch
-
 8:30
8:30
for better cyber security response, how do you utilize blackberry athoc?
-
 3:56
3:56
gary davis, blackberry | zero trust summit 2022
-
 1:59
1:59
increase cybersecurity agility and cyber resilience
-
 35:04
35:04
ai powered bladerunners: the role of ai in implementing zero trust
-
 19:48
19:48
ztna best practices
-
 37:15
37:15
blackberry’s cybersecurity platform evolves
-
 1:10
1:10
endpoint protection and prevention: a customer success story based on true events
-
 9:58
9:58
accelerate zero trust cybersecurity adoption with powerstore
-
 0:16
0:16
zero trust and ai: the future of cybersecurity 15s
-
 7:38
7:38
implementing zero trust with proactive resiliency
-
 1:47
1:47
blackberry mdr | realize the benefits of cylanceguard
-
 1:52
1:52
stop more cyberattacks, faster, with less effort | blackberry cybersecurity
-
 1:50
1:50
blackberry prevents 3cx zero-day attack