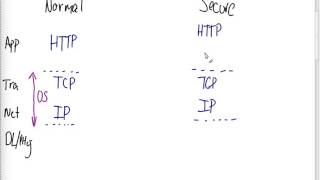
insecurity of http (its335, l19, y15)
Published 8 years ago • 595 plays • Length 13:10Download video MP4
Download video MP3
Similar videos
-
 39:26
39:26
https and ssl/tls (its335, l19, y15)
-
 23:48
23:48
review of cryptography assumptions (its335, l19, y15)
-
 27:44
27:44
browsing, http and web applications (its335, l18, y15)
-
 35:02
35:02
proxies and firewall locations (its335, l18, y15)
-
 1:01:16
1:01:16
mitm attack and digital certificates (its335, l20, y15)
-
 46:38
46:38
attacks on digital certificates (its335, l21, y15)
-
 1:37:31
1:37:31
introduction to it security (its335, l1, y14)
-
 23:53
23:53
cure for the insecure - joyce meyer | icln
-
 3:17
3:17
how to remove google search results of my name | remove personal information from google search
-
 48:27
48:27
packet filter firewall examples (its335, l16, y15)
-
 1:13:58
1:13:58
salted passwords and rainbow tables (its335, l07, y15)
-
 1:21:34
1:21:34
symmetric key encryption and brute forece (its335, l3, y14)
-
 1:15:50
1:15:50
authentication with symmetric key ciphers (its335, l4, y14)
-
 1:09:04
1:09:04
web browsing and https (its335, l20, y14)
-
 1:16:05
1:16:05
web attacks, owasp top 10 and cookies (its335, lecture 22, 2013)
-
 1:13:17
1:13:17
web security and https (its335, l21, y14)
-
 11:08
11:08
unvalidated redirect attack (its335, l25, y14)
-
 1:19:07
1:19:07
authentication with hash functions (its335, l05, y14)
-
 1:13:29
1:13:29
web security attacks (its335, l24, y14)
-
 6:56
6:56
insecure women are attacking other women every way woman talk show
-
 57:09
57:09
encryption techniques (its335, l2, y14)