internet vulnerability
Published 4 months ago • 13 plays • Length 7:28Download video MP4
Download video MP3
Similar videos
-
 47:12
47:12
end-to-end analysis of a domain generating algorithm malware family
-
 1:01:44
1:01:44
vacuum robot security and privacy
-
 38:08
38:08
defending dram for data safety and security in the cloud with dr. stefan saroiu | podcast
-
 10:55
10:55
dr.r.suganya|windows hacking|dr.r.suganya
-
 9:49
9:49
dr.r.suganya|cybersecurity awareness|drsnsrcas
-
 12:48
12:48
dr.r.suganya|authentication function|sns institutions
-
 6:53
6:53
dr.r.suganya|scanning|sns institutions
-
 6:17
6:17
dr.r.suganya|malware infection|sns institutions
-
 8:09
8:09
dr.r.suganya|pgp|sns intitutioins
-
 4:49
4:49
sns vision story telling-dr.r.suganya
-
 6:15
6:15
dr.r.suganya|ransomeware|sns institutions
-
 5:03
5:03
dr.r.suganya|unauthorized access|sns institutions
-
 7:07
7:07
dr.r.suganya|digital certificates|sns instituions
-
 6:02
6:02
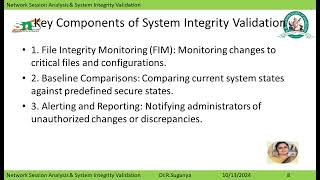
dr.r.suganya|network session analysis, system integrity validation|sns institutions
-
 6:08
6:08
dr.r.suganya|malware|sns institutions
-
 9:25
9:25
dr.r.suganya|cracking|sns institutions