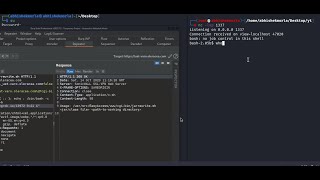
intro to command injection | security simplified
Published 3 years ago • 952 plays • Length 2:45Download video MP4
Download video MP3
Similar videos
-
 6:39
6:39
they are all injection vulnerabilities! - security simplified
-
 9:27
9:27
how to conduct a basic security code review | security simplified
-
 3:57
3:57
how to prevent command injections
-
 9:44
9:44
sql injection prevention: security simplified
-
 5:33
5:33
what is sql injection? -- security simplified
-
 3:54
3:54
how to do command injection attack?
-
 11:07
11:07
operating system command injection tutorial
-
 2:41
2:41
$9060 os command injection poc | private bug bounty program 2023 | p1 insecure os firmware
-
 5:27
5:27
wildcard injection privilege escalation: linux security 07
-
 2:51
2:51
system command injection - explained
-
 7:35
7:35
understanding insecure deserialization vulnerabilities: security simplified
-
 3:04
3:04
how to prevent idors | security simplified
-
 13:05
13:05
getting started with command injection
-
 4:27
4:27
exploiting php type juggling vulnerabilities - security simplified
-
 1:21:09
1:21:09
introduction to os command injections - full course
-
 9:21
9:21
how to learn anything in computer science or cybersecurity | security simplified
-
 7:46
7:46
what is command injection? - web security academy
-
 6:26
6:26
command injection explained
-
 6:15
6:15
misconfigured path privilege escalation: linux security 06
-
 32:07
32:07
command injection | complete guide
-
 2:17
2:17
command injection vulnerabilities - roman explains