asymmetric encryption - simply explained
Published 6 years ago • 1.3M plays • Length 4:40Download video MP4
Download video MP3
Similar videos
-
 15:28
15:28
intro to asymmetric key cryptography
-
 21:21
21:21
symmetric key cryptography and asymmetric key cryptography | cryptography tutorial | simplilearn
-
 8:23
8:23
lec-83: asymmetric key cryptography with example | network security
-
 10:31
10:31
asymmetric key cryptography | rsa encryption algorithm | asymmetric encryption | simplilearn
-
 7:23
7:23
#27 principles of asymmetric key cryptography |cns|
-
 8:40
8:40
the rsa encryption algorithm (1 of 2: computing an example)
-
 3:35
3:35
symmetric and asymmetric key cryptography
-
 8:46
8:46
asymmetric key cryptography
-
 13:34
13:34
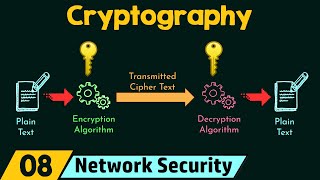
cryptography
-
 13:58
13:58
encryption - symmetric encryption vs asymmetric encryption - cryptography - practical tls
-
 6:31
6:31
introduction to secure hash algorithm sha 512 || lesson 74 || cryptography ||
-
 6:14
6:14
lec-81: symmetric key cryptography in network security with examples
-
 8:00
8:00
intro to asymmetric public key cryptography | rsa encryption
-
 2:20
2:20
asymmetric cryptosystems - applied cryptography
-
 7:04
7:04
mathematical cryptosystems (2 of 2: asymmetric cryptography)
-
 15:08
15:08
secure hash algorithm -number theory and asymmetric key cryptography - data compression & encryption
-
 12:58
12:58
rsa algorithm with example | asymmetric key cryptography (public key cryptography)
-
 4:53
4:53
asymmetric key cryptography rsa
-
 10:08
10:08
asymmetric key cryptography: the rsa algorithm by hand