isolate compromised host using 5-tuple
Published 1 year ago • 49 plays • Length 22:33Download video MP4
Download video MP3
Similar videos
-
 8:42
8:42
isolate compromised host using 5-tuple
-
 12:14
12:14
lab - isolate compromised host using 5-tuple
-
 40:30
40:30
12.4.1.2 alt lab - isolate compromised host using 5-tuple
-
 29:00
29:00
lab - isolate compromised host using 5-tuple
-
 39:49
39:49
12 4 1 2 lab - isolate compromised host using 5 tuple
-
 19:32
19:32
lab 27 2 14 isolate compromised host using 5 tuple
-
 20:30
20:30
modul 27.2.14 - lab - isolate compromised host using 5-tuple
-
 1:04:10
1:04:10
12.4.1.2 lab - isolate compromised host using 5-tuple
-
 12:59
12:59
lab 27.2.15 investigating a malware exploit
-
 52:39
52:39
cts 340: wi-fi 7, mlo, and preamble puncturing (sponsored)
-
 1:03:58
1:03:58
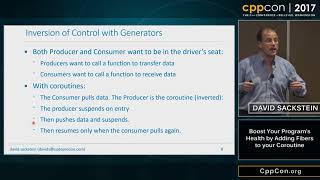
cppcon 2017: david sackstein “boost your program’s health by adding fibers to your coroutine”
-
 34:33
34:33
27.2.14 lab - isolate compromised host using 5 tuples
-
 55:05
55:05
lab 27.2.14 - isolate compromised host using 5-tuple - ilm - herianto
-
 36:35
36:35
topik 9 lab isolate compromised host using 5 tuple
-
 1:27:59
1:27:59
lab – isolated compromised host using 5-tuple
-
 15:14
15:14
12.4.1.2 lab - isolate compromised host using 5-tuple
-
 24:16
24:16
interpret http and dns data to isolate threat actor
-
 41:29
41:29
12 4 1 2 alt lab isolate compromised david