keystone jws tokens past, present, and future
Published 5 years ago • 340 plays • Length 34:49Download video MP4
Download video MP3
Similar videos
-
 43:10
43:10
deep dive into keystone tokens and lessons learned
-
 10:46
10:46
learn about keystone to keystone federation and see it work with horizon for ocata
-
 40:18
40:18
keystone security and architecture review
-
 1:07
1:07
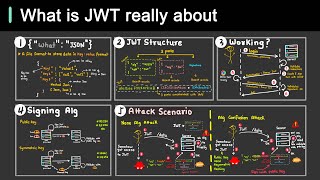
how does jwt work
-
 2:18
2:18
session vs token authentication in 100 seconds
-
 7:00
7:00
session vs jwt: the differences you may not know!
-
 5:14
5:14
why is jwt popular?
-
 3:57
3:57
apis explained (in 4 minutes)
-
 41:15
41:15
keystone advanced authentication methods
-
 33:37
33:37
one keystone to rule them all
-
 32:50
32:50
state of the project keystone
-
 37:19
37:19
secure keystone deployment: lessons learned and best practices
-
 18:25
18:25
project update - keystone
-
 24:46
24:46
bridging clouds with keystone to keystone federation
-
 28:35
28:35
keystone - project update
-
 14:53
14:53
what is jwt and why should you use jwt
-
 37:10
37:10
keystone to keystone federation
-
 39:41
39:41
federated access to openstack via keystone v3 api
-
 4:24
4:24
securing rest apis - jwt token explained in 4 minutes for beginners tutorial - s27e01
-
 12:06
12:06
ptl overview: keystone
-
 43:00
43:00
integrating keystone with large-scale centralized authentication.
-
 31:09
31:09
highly resilient, multi-region keystone deployments