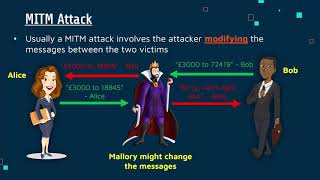
man in the middle attack
Published 4 years ago • 63 plays • Length 0:40Download video MP4
Download video MP3
Similar videos
-
 1:20
1:20
what is a man-in-the-middle attack? (in about a minute)
-
 11:54
11:54
how to set up a man in the middle attack | free cyber work applied series
-
 13:29
13:29
man in the middle attacks & superfish - computerphile
-
 7:10
7:10
man in the middle attack mitm using wireshark and ettercap | full tutorial for beginner 2022
-
 9:50
9:50
the attack that could disrupt the whole internet - computerphile
-
 9:18
9:18
key exchange problems - computerphile
-
 2:53
2:53
score's ai integration strengthens counter-terrorism, says foreign ministry
-
 3:54
3:54
man-in-the-middle attack explained: how can you to prevent mitm attack
-
 5:52
5:52
what is a man-in-the-middle attack?
-
 11:35
11:35
arp poisoning | man-in-the-middle attack
-
 3:08
3:08
meet in the middle attack
-
 19:07
19:07
how hackers sniff (capture) network traffic // mitm attack
-
 2:41
2:41
what is a man-in-the-middle attack?
-
 4:13
4:13
man-in-the-middle attacks
-
 0:44
0:44
cybersecurity dictionary - man in the middle attack
-
 1:54
1:54
man-in-the-middle attacks explained | nordvpn
-
 2:35
2:35
man in the middle attacks with free wi-fi
-
 1:00
1:00
how man-in-the-middle attacks works #shorts
-
 1:15
1:15
rcs allows mitm attack -- messages can be intercepted and modified
-
 1:58
1:58
detect and prevent man-in-the-middle attack