meet-in-the-middle attack (css441, l07, y15)
Published 8 years ago • 7.6K plays • Length 1:18:36Download video MP4
Download video MP3
Similar videos
-
 52:31
52:31
meet-in-the-middle attack on double block cipher
-
 1:22:15
1:22:15
des and meet-in-the-middle attack (css322, l6, y14)
-
 1:09:21
1:09:21
transposition ciphers and steganography (css441, l04, y15)
-
 3:08
3:08
meet in the middle attack
-
 17:15
17:15
basics of encryption (css441, l01, y15)
-
 1:08:56
1:08:56
classical substitution ciphers (css441, l03, y15)
-
 9:18
9:18
key exchange problems - computerphile
-
 11:35
11:35
arp poisoning | man-in-the-middle attack
-
 11:46
11:46
ss7 message interception
-
 18:09
18:09
digital signatures (css441, l18, y15)
-
 46:39
46:39
data encryption standard (css441, l06, y15)
-
 1:29:57
1:29:57
cryptographic hash functions (css441, l17, y15)
-
 1:04:50
1:04:50
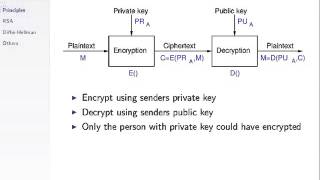
public key cryptography (css441, l13, y15)
-
 1:13:49
1:13:49
caesar cipher for encryption (css441, l02, y15)
-
 1:15
1:15
rcs allows mitm attack -- messages can be intercepted and modified
-
 15:24
15:24
iphone and android wifi man-in-the-middle attack // python scapy scripts for attacking networks
-
 11:47
11:47
man in the middle attack in diffie hellman key exchange | prevention against man in middle attack
-
 3:27
3:27
egco342: mitm attack
-
 1:07:56
1:07:56
public key crypto with rsa (css441, l12, y15)
-
 7:10
7:10
man in the middle attack mitm using wireshark and ettercap | full tutorial for beginner 2022
-
 2:02
2:02
cyber security agenda - 5 ) mitm attack