memory forensics: how we used to do it & how we use it to respond to large-scale breaches today
Published 1 year ago • 3K plays • Length 20:41Download video MP4
Download video MP3
Similar videos
-
 27:26
27:26
memory forensics at a scale
-
 36:31
36:31
making memories: using memory analysis for faster response to user investigations - sans dfir summit
-
 31:30
31:30
finding evil in windows 10 compressed memory
-
 1:13:09
1:13:09
sans dfir webcast - introduction to windows memory analysis
-
 2:59
2:59
episode 74: how to get started in digital forensics
-
 57:53
57:53
handling ransomware incidents: what you need to know!
-
 58:20
58:20
for572: always updating, never at rest
-
 58:07
58:07
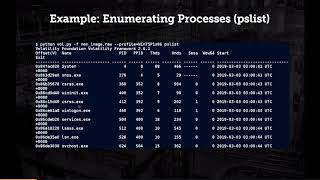
analyzing user mode dumps with windbg
-
 1:03:22
1:03:22
investigating malware using memory forensics - a practical approach
-
 3:59
3:59
3 ways to get sans giac certified cheaper
-
 1:04:28
1:04:28
memory forensics acquisition cloud
-
 1:08:10
1:08:10
sans dfir webcast - memory forensics for incident response
-
 29:33
29:33
diy dns dfir: you’re doing it wrong: threat hunting summit 2016
-
 3:35
3:35
all you need to know about for500 - windows forensic analysis with jason jordaan
-
 5:59
5:59
malware blocks - sans dfir summit
-
 22:20
22:20
how to use cti, no matter the size of your organization
-
 26:05
26:05
what would you say you do here?: redefining the role of intelligence in investigations
-
 47:10
47:10
applying ds/ml to forensics and incident response: an interview with jess garcia
-
 28:28
28:28
processing pci track data with cdpo - sans digital forensics & incident response summit 2017
-
 55:42
55:42
bridging the gap between mobile and computer forensics
-
 53:44
53:44
introducing the enterprise cloud forensics & incident response poster