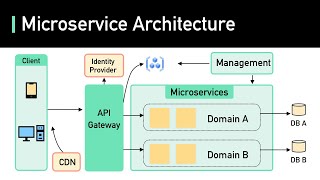
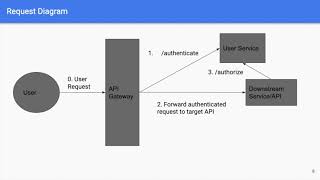
microservices identity & authorization
Published 6 years ago • 7.5K plays • Length 10:47Download video MP4
Download video MP3
Similar videos
-
 10:03
10:03
microservices authentication/authorization architectural pattern
-
 8:02
8:02
microservices security architecture ( cybersecurity basics)
-
![example of microservice to microservice authentication [c#/.net]](https://i.ytimg.com/vi/sVIDQCDETLo/mqdefault.jpg) 11:55
11:55
example of microservice to microservice authentication [c#/.net]
-
 17:47
17:47
the problem with microservices
-
 20:52
20:52
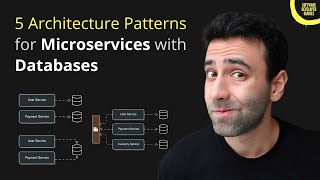
microservices with databases can be challenging...
-
 4:45
4:45
what are microservices really all about? (and when not to use it)
-
 5:01
5:01
authentication & authorization in microservice architectures
-
 20:33
20:33
microservices security | best practices to secure microservices | edureka
-
 50:26
50:26
authentication as a microservice
-
 5:17
5:17
microservices explained in 5 minutes
-
 3:31
3:31
microservices: pros and cons - cassandra shum (thoughtworks) & rachel laycock (thoughtworks)
-
 53:19
53:19
authentication and authorization in a cloud and microservice world by stefan reuter and thomas kruse
-
 1:04:36
1:04:36
building secure microservices in azure - jimmy bogard - ndc london 2023
-
 39:45
39:45
security patterns for microservice architectures
-
 1:25:32
1:25:32
microservices security using jwt | spring cloud gateway | javatechie
-
 5:58
5:58
securing #microservices using #apigateway | #authentication & #authorisation in #microservices
-
 1:00:13
1:00:13
how to secure your microservices architecture with json web tokens
-
 33:45
33:45
an authentication and authorization architecture for a microservices world — david ferriera
-
 8:49
8:49
authentication and authorization in a microservice architecture | oauth 2.0 | jwt
-
 0:34
0:34
microservices should not share code #shorts #microservices
-
 28:29
28:29
authorization in a distributed / microservice system | .net conf 2022