monitoring privilege creep across your cloud infrastructure
Published 3 years ago • 710 plays • Length 8:07Download video MP4
Download video MP3
Similar videos
-
 5:52
5:52
protect your aws infrastructure by right-sizing your identities' privileges
-
 6:29
6:29
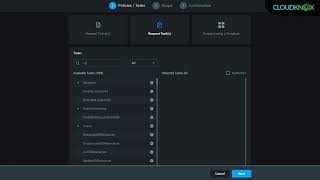
the cloudknox platform privilege on-demand workflow
-
 6:05
6:05
protect your infrastructure by right sizing your identities' privileges
-
 3:45
3:45
4 keys to securing the cloud with privileged access
-
 0:32
0:32
aws cloud infrastructure security findings from cloudknox
-
 28:00
28:00
integrated security for application & cloud operations
-
 5:12
5:12
what is cloud infrastructure entitlement management (ciem)? a key cloud access solution
-
 7:00
7:00
top 3 access risks in cloud security
-
 13:25
13:25
how to achieve zero trust at cloud scale with cloud infrastructure entitlement management (ciem)
-
 0:33
0:33
vmware cloud infrastructure security findings from cloudknox
-
 2:01
2:01
cloudknox overview
-
 20:53
20:53
a zero trust approach to cloud infrastructure
-
 2:39
2:39
securing the cloud with cyberark privileged access security
-
 2:27
2:27
totvs secures aws cloud console and assets with cyberark privileged access security
-
 27:49
27:49
uncover 5 hidden risks that can expand your cloud infrastructure attack surface
-
 5:31
5:31
cloudknox compliance dashboard and reports
-
 1:15
1:15
privileged access cloud security
-
 43:13
43:13
the magic behind cloud infrastructure security
-
 43:56
43:56
all aboard podcast: episode 8: how hashicorp achieved least privilege through just-in-time access
-
 51:16
51:16
challenges protecting privileged credentials in cloud environments
-
 34:37
34:37
identifying toxic combinations of permissions in your cloud infrastructure - michael raggo